Image XSS is very interesting concept...Inspired by Saumil Shah's one of video, I decided to try it out and it worked well!..Interesting!..
Just for reference am putting these things here on my blog.
First this we will need simple "GIF" Extension File, why????? because it simply starts with : GIF89a
Anything after this will be your actual GIF Image file contents.
Idea here is to create our GIF file in such a way that it will be valid file as well as it should have Malicious Javascript embedded into..!
If we create GIF file (test.gif) as below through Hex Editor :
If it would be Java Script, GIF89a will be considered as a Variable, /*....../* will be comments
=0 will be assigned to GIF89a .... which means....there are 2 Lines of javascript code, 1 for assigning value 0 to variable and second part after semi colon will act as malicious script!!!
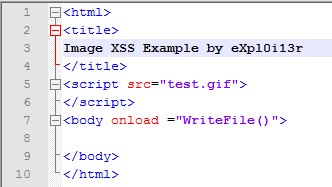
But currently it is just an Image!....not a java script...what if we create test.html file with below content :
Now you can place all pieces together and will get something like :
<script src="GIF89a/*.......*/=0;alert("eXploi13r Here")">
It is self explanatory...!!!!
Be aware, simple GIF Images may contain, malicious scripts....!!! :)